A friend recently challenged me with the following hypothesis: Open source is something that is valuable to programmers but when programmers are writing open source software they have no incentive to build software that is useful for end users. Because of this, we we end up with overly complex software that may not even address the need of the end users and hence the original intent of the project.
After thinking about this for awhile I have decided that I agree that there is a serious disconnect between software developers and end users, but I don't think open source has much to do with it. Programmers are good at logical thinking (without emotion), understanding complex documentation (pages of text), and holding multiple concepts and equations in their heads at the same time. In fact they tend to thrive on this kind of stuff. Case in point, I was just looking at a product that allows you to remotely control someone else's PC. Let's have a look at two images on their site:

Whether you are a computer programmer or not, that is a terrible attempt to communicate something. The only thing it communicates to me is that this setup is complex. Perhaps that is how the programmer's mind visualizes what he is building, and that is fine, but let's keep our private parts (brain dumps included) to ourselves, eh?

I thought this second image (they are both on the same page) was pretty funny. Instead of explaining that the software can help your mom when she "loses the internet" by letting you control her computer from afar, the developer decides to show you how you can recursively connect to yourself and create an infinite number of desktops within desktops. "Whoa dude, isn't it crazy what I can do?? I feel like my brain is going to explode!" Sorry, elite hacker dude, it's not cool. It's lame and I am sorry that normal people will never use your software because most people don't like software that makes their brain explode, they like things that help mom. Most people, but not computer programmers. The more head-xplode-dacious the better for geeks!
This problem gets compounded when you have programmers in DC "solving" problems in Africa or the Philippines. Not only do we have the programmer/normal person gap, but we also have a cultural gap (take it from me, never use the word stupid in the Philippines) and a geographical gap (body language and timezones matter). The greater the gap, then the more useless the stuff we end up with is. The more time programmers spend in country the more we can reduce this gap. Or even better, find some
programmers from the country itself. This can improve things a lot, but you still have the classic gap between programmers and end users.
The way to solve this is to have programmers never design anything that a user will see, ever. Instead you have designers design stuff and programmers implement it. Back in the dot com days I worked for a
big technology consulting firm and every project had at least one business strategy person, a designer and a computer programmer. We created some world changing stuff, but we were expensive, spent a lot of money on flashy artsy offices and flamed out. But I worked with designers and learned to understand their value (and my own shortcomings in that area).
Macs and iphones aren't programmed in California - they are Designed (check the back of your iphone). I hear that Apple has heavily relied on their Silicon neighbor IDEO to do a lot of their design work, or more likely they probably just hired a bunch of IDEO people. IDEO is a pure design firm, they spend most of their time watching and talking with users, and the other part of their time is spent trying to think outside the box by crossing and combining design patterns from disparate genres and seeing if they can come up with something useful. I just installed an iphone app called Party Whistle designed by the IDEO guys. It is the antithesis of the above examples:

When you launch the app you see a party whistle on the screen, and a little icon recommending that you blow into one end of your phone. When you do his, the whistle expands and makes funny noises and all sorts of wacky stuff. Emphasis on wacky. Nothing useful. It doesn't help plan a party or coordinate party favors, it is just wackyness designed elegantly and simply. This is what you get without programmers.
What we really need is to take the brilliant visual ideas of designers and connect them with innovative plumbing that programmers do.
Usually we do this backwards, and we give the problem to the programmer and they plumb it, then they make it so that they can use it, then they try and make it look nice. With a single designer or artist or business plan you have nothing. But with a single programmer you can usually create
something, even if that something is just a shadow of what it could be. It's this shadow world of foggy potential that the programmers tend to fester.
How does this relate to open source? It doesn't really. The best programmers hate to create boring stuff like menus and reminder windows because all of that stuff has been done before. They would rather reuse someone else's code so they could focus on doing the really challenging (brain exploding?) part. This is how programmers are wired, so if they aren't allowed to use open source they will be less happy and will be forced to waste their time on reinventing the wheel. Whether it is open or not will have no impact on usability.
Open source lets programmers stand on the shoulders of giants and build the stuff that they think is important and cool. As a result open source has little to do with cost (of any kind) and more to do with creating an easy way for programmers to share, communicate and collaborate. I prefer working with open source software because I can find other developers trying solve the same problems on
IRC. I can google for documentation and wiki my own thoughts to it so that others benefit and see how cool I am. I can join mailing lists. It also means that open source programmers write their code so that others can read it and use it and modify it easily. All of this leads to high-productivity, innovation and personal fulfillment for open sourcers.
It doesn't lead to good user centric design.
Yet open source programmers are figuring out good ways to work together. Open source fosters that, and that is why the innovation is coming out of open source. Open source enables programmers to work on the innovative stuff. Tools like
cucumber (story based testing) and
github (facebook for geeks) and others are further helping programmers spend their time on innovation, and less on the debugging and already solved problems.
The challenge then is to figure out how to use the open source approach so that it can bridge the geeks with the artists. Imagine if designers could easily express their prototypes without having to waste a lot of time explaining it to programmers. When artists can hook into code as easily as they can doodle a design, then we will have a renaissance that spreads beyond just the geek elite.



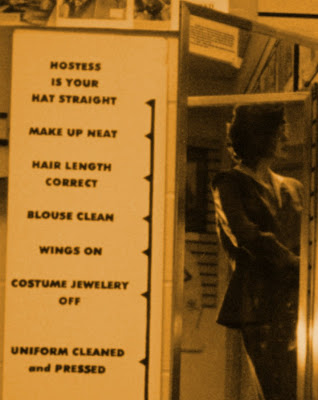







 [/caption]
[/caption]

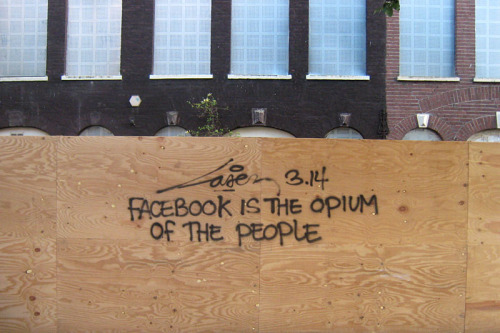
 (Image by Jösé@flickr)
(Image by Jösé@flickr)